How to Choose MCP Authentication Solutions and Top 5 Solutions in 2026
What Are Model Context Protocol (MCP) Authentication Solutions?
MCP authentication solutions are mechanisms used to control access between MCP clients and MCP servers. Since MCP enables AI systems to connect to external tools, data sources, and workflows, authentication ensures that only authorized clients and users can interact with those resources.
Choosing Model Context Protocol (MCP) authentication solutions requires balancing security requirements with user experience, specifically determining whether to use shared credentials or individual user permissions. The current best practice is to align with OAuth 2.1, which provides standardized, secure, and user-aware access control.
MCP does not enforce a single authentication method. Instead, it follows established standards (primarily OAuth-based flows) to create trust between clients and servers. This approach allows MCP to integrate with existing identity systems while securing access to sensitive operations and data.
Authentication becomes important when MCP servers expose user data, administrative actions, or enterprise systems. In these cases, the server must verify identity and permissions before allowing requests.
In this article:
Core Authentication Mechanisms in MCP
OAuth 2.1
OAuth 2.1 is the primary authorization framework used in MCP. It defines how clients obtain access tokens that grant permission to call MCP server endpoints.
The flow starts when a client attempts to connect to a protected server and receives a 401 response with metadata about the authorization process. The client then discovers the authorization server, registers itself, and redirects the user to log in and approve access.
After user consent, the client receives an access token, which is included in future requests. The MCP server validates this token before processing any operation. This ensures that only authorized clients can access protected tools and resources.
OpenID Connect (OIDC)
OIDC is used alongside OAuth for identity discovery and metadata retrieval. During the authorization process, MCP clients fetch configuration details from OIDC discovery endpoints exposed by the authorization server.
These endpoints provide information such as authorization URLs, token endpoints, and issuer details. This allows the client to understand how to authenticate without hardcoding configuration.
In MCP, OIDC plays a supporting role by standardizing how identity and authorization server capabilities are discovered.
Machine-to-Machine OAuth (Client Credentials Flow)
Machine-to-machine (M2M) authentication in MCP is implemented using the OAuth 2.0 client credentials flow. This method applies to scenarios where no human user is involved, such as backend services, automation pipelines, or system integrations.
In this flow, the client authenticates directly with the authorization server using its own credentials, usually a client ID and client secret or a signed JWT. The authorization server validates these credentials and issues an access token representing the application itself, not a user.
The client then includes this token in requests to the MCP server, which verifies it before granting access. Because there is no user context, permissions are typically scoped to the application or service account.
In MCP, this flow is commonly used for:
- Server-to-server integrations
- Background jobs and scheduled tasks
- CI/CD pipelines and automation tools
This approach allows secure, non-interactive access while maintaining control over what each service can do.
Mutual TLS (mTLS) for Service-to-Service Auth
Mutual TLS (mTLS) is an authentication mechanism used in MCP for securing communication between services at the transport layer. Unlike OAuth, which operates at the application layer using tokens, mTLS verifies the identity of both the client and the server using digital certificates during the TLS handshake.
In an mTLS setup, both parties present X.509 certificates issued by a trusted certificate authority. Each side validates the other’s certificate before establishing a connection.
Within MCP architectures, mTLS is often used to:
- Strengthen security for internal service-to-service communication
- Protect sensitive enterprise environments and private networks
- Complement OAuth by adding a second layer of trust
When combined with OAuth, mTLS provides layered protection. OAuth ensures proper authorization and scoping, while mTLS confirms that the communicating parties are trusted systems.
How to Choose MCP Authentication Solutions
Here are some of the main factors to look out for when selecting an MCP authentication solution.
Architecture Fit (Local vs. Remote MCP)
Authentication requirements differ depending on whether the MCP server runs locally or remotely. Early MCP setups often ran client and server on the same machine, where authentication was minimal because there was no network boundary or third-party access involved.
As soon as MCP servers are exposed over a network, stronger authentication becomes necessary. Remote deployments require OAuth-based authorization to let users grant access without sharing credentials, especially when third-party clients act on their behalf.
For local setups, simpler mechanisms such as environment-based credentials may be sufficient. For remote or enterprise systems, OAuth with token validation and identity separation becomes necessary to prevent unauthorized access and data leakage.
Identity Provider (IdP) Integration
MCP is designed to work with existing identity providers rather than introducing a new authentication system. The authorization server (IdP) handles user login, consent, and token issuance, while the MCP server acts as a resource server that validates those tokens.
Using an external IdP simplifies implementation and aligns with enterprise security practices. It centralizes identity management, supports features like single sign-on, and reduces the need to build custom authentication flows.
Alternatively, embedding an authorization server inside the MCP system gives full control but increases complexity. Teams must implement login flows, consent handling, and secure token issuance themselves, which adds operational and security overhead.
Token Management and Scope Design
Tokens are central to MCP authentication. Clients obtain access tokens through OAuth flows and include them in requests, while MCP servers validate these tokens and enforce permissions.
Two main token formats are used: JWTs, which allow local validation using embedded claims, and opaque tokens, which require lookup in a data store. Each has trade-offs between performance and revocation control.
Scopes define what actions a client can perform. In MCP, scopes should map to tools or operations rather than coarse API access. Fine-grained scopes improve security and reduce unnecessary permission prompts, but they require careful design to avoid complexity and user friction.
Observability, Auditing, and Compliance
Authentication in MCP must support logging and traceability. Each authenticated request should be tied to a user identity, client, and granted scopes, enabling auditing of actions performed through MCP tools.
Logging token usage, failed validations, and insufficient scope errors helps detect misuse and supports compliance requirements. This is especially important in enterprise environments where regulatory standards require visibility into who accessed what data and when.
Additional considerations include tracking consent grants, monitoring token lifecycles, and ensuring that access can be revoked when needed.
Security Posture and Threat Protection
MCP authentication must address risks including unauthorized access, token misuse, and data exposure. Remote MCP servers introduce new attack surfaces, especially when interacting with external tools and APIs.
OAuth 2.1 mitigates many of these risks through mechanisms like PKCE, scoped access, and short-lived tokens. MCP also enforces practices such as validating token audience and preventing token passthrough to downstream services to avoid confused deputy attacks.
Additional protections include enforcing HTTPS, applying network restrictions, and using managed identities instead of static API keys to reduce credential exposure.
Developer Experience and Integration Complexity
MCP authentication introduces complexity due to OAuth flows, token handling, and discovery mechanisms. Developers must implement features such as protected resource metadata, authorization server discovery, and token validation.
Using external identity providers and standardized discovery endpoints reduces this burden by allowing clients to dynamically configure authentication without hardcoding endpoints.
However, challenges remain, including token lifecycle management, dynamic client registration, and handling edge cases like expired tokens in persistent connections. These factors increase implementation effort, especially in distributed systems.
Extensibility and Future-Proofing
MCP authentication is built on widely adopted standards like OAuth 2.1, which makes it adaptable as the ecosystem evolves. This allows implementations to benefit from improvements in the broader OAuth and identity landscape.
The specification continues to evolve, with proposals around client trust, server-side authorization handling, and improved scope discovery. Designing systems with external IdPs, standard token validation, and modular components makes it easier to adopt these changes over time.
Future-proof implementations should avoid tightly coupling authentication logic to MCP servers and instead rely on interoperable standards, ensuring compatibility with new tools, identity systems, and security requirements.
Top Solutions that Meet These Criteria
1. Obot

Obot provides an MCP-native authentication layer designed to simplify how AI agents securely access tools, APIs, and enterprise systems. It focuses on bridging OAuth-based identity systems with MCP workflows, enabling user-aware and service-level authentication without requiring complex custom implementations.
Key features include:
- OAuth 2.1–aligned authentication: Implements standardized authorization flows for both user and machine-to-machine access
- Built-in identity abstraction: Connects MCP servers to external identity providers without tightly coupling to a specific vendor
- Fine-grained access control: Maps scopes and permissions directly to MCP tools and operations
- Token lifecycle management: Handles token issuance, validation, and refresh workflows to reduce developer overhead
- Agent-aware authentication: Supports both user-delegated and autonomous agent access patterns within MCP environments
How it meets the criteria:
- Architecture fit: Designed for both local and remote MCP deployments, with strong support for distributed and multi-agent systems.
- IdP integration: Flexible, allowing integration with existing OAuth/OIDC providers while abstracting implementation complexity.
- Token management and scopes: Emphasizes fine-grained, tool-level scopes with built-in handling of token validation and lifecycle.
- Observability and auditing: Provides visibility into agent actions and token usage, enabling traceability across MCP workflows.
- Security posture: Strong, with OAuth 2.1 alignment, scoped access, and support for secure agent-to-service interactions.
- Developer experience: High, as it reduces the need to manually implement authentication flows while remaining flexible for customization.
2. Keycloak

The Keycloak MCP server connects MCP-based workflows with an existing identity and access management system. It exposes administrative operations such as user and realm management through MCP tools, allowing AI agents to perform identity-related actions programmatically. This approach integrates MCP with centralized identity control, rather than introducing a separate authentication layer.
Key features include:
- User and realm management tools: Provides MCP-accessible operations for creating, deleting, and listing users and realms
- Integration with existing identity systems: Uses Keycloak as the underlying identity provider for authentication and authorization
- Administrative automation: Enables AI agents to perform identity management tasks programmatically
- Environment-based configuration: Uses standard credentials and environment variables for connecting to Keycloak instances
- MCP-compatible interface: Works with MCP clients to expose identity operations as structured tools
How it meets the criteria:
- Architecture fit: Works well for remote MCP deployments with centralized identity, but less suited for lightweight or local setups due to operational overhead.
- IdP integration: Strong, as it is itself a full identity provider, though this adds complexity if an organization already uses another IdP.
- Token management and scopes: Mature support for tokens and fine-grained roles, but mapping scopes cleanly to MCP tools may require customization.
- Observability and auditing: Provides audit logs and session tracking, though extracting MCP-specific insights may require additional tooling.
- Security posture: Strong, with support for OAuth, OIDC, and advanced security controls, but misconfiguration risk is high due to system complexity.
- Developer experience: Powerful but complex, with a steeper learning curve and more setup compared to lightweight solutions.
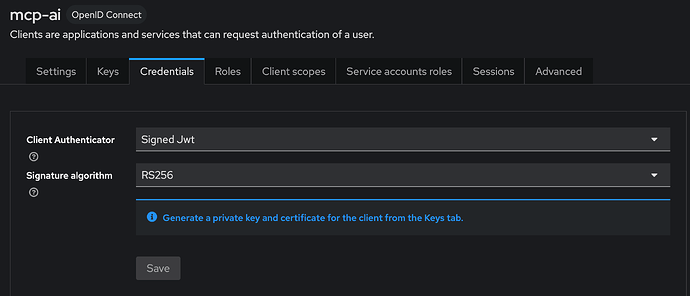
Source: Keycloak
3. MCP Auth

MCP Auth is a library that helps simplify adding authentication to MCP servers by implementing OAuth 2.1 flows and token validation patterns. It focuses on reducing the complexity of integrating authentication by providing reusable components that align with MCP specifications and identity provider standards.
Key features include:
- OAuth 2.1 integration: Implements standardized authorization flows for secure access control
- Provider-agnostic design: Works with any compliant OAuth or OpenID Connect identity provider
- JWT-based authentication: Supports token validation and claim extraction for authorization decisions
- Protected resource metadata support: Exposes authentication requirements for automatic client discovery
- Minimal integration overhead: Adds authentication with a small amount of configuration and code
How it meets the criteria:
- Architecture fit: Well-suited for embedding into MCP servers, but not a full standalone authentication system.
- IdP integration: Strong, as it is provider-agnostic and works with any OAuth/OIDC provider.
- Token management and scopes: Handles JWT validation and standard flows, though advanced lifecycle management depends on the external IdP.
- Observability and auditing: Limited built-in capabilities; relies on external systems for logging and monitoring.
- Security posture: Solid baseline with OAuth 2.1 alignment, but lacks advanced enterprise protections out of the box.
- Developer experience: High, as it reduces implementation effort, though teams still need to understand OAuth concepts.
4. Azure MCP Server
Azure MCP Server integrates MCP with Azure’s identity and access management system, enabling AI agents to securely interact with Azure resources. It uses Entra ID and role-based access control to enforce permissions, aligning MCP authentication with enterprise identity practices.
Key features include:
- Entra ID authentication: Uses Azure’s identity platform for secure user and service authentication
- Role-based access control: Applies fine-grained permissions using Azure RBAC
- Managed identity support: Allows secure access without exposing static credentials
- Integration with Azure tools and services: Connects MCP workflows to Azure CLI and resource APIs
- Multi-environment support: Works across development tools, languages, and enterprise environments
How it meets the criteria:
- Architecture fit: Strong for cloud-based and enterprise deployments, but tightly coupled to Azure environments.
- IdP integration: Excellent, with native Entra ID integration and enterprise-grade identity management.
- Token management and scopes: Robust, leveraging Azure’s token services and RBAC, though scope design is tied to Azure models.
- Observability and auditing: Strong, with built-in logging, monitoring, and compliance tooling.
- Security posture: High, including managed identities and enterprise security controls, but dependent on Azure ecosystem.
- Developer experience: Good within Azure, but less portable and harder to use in multicloud or non-Azure setups.
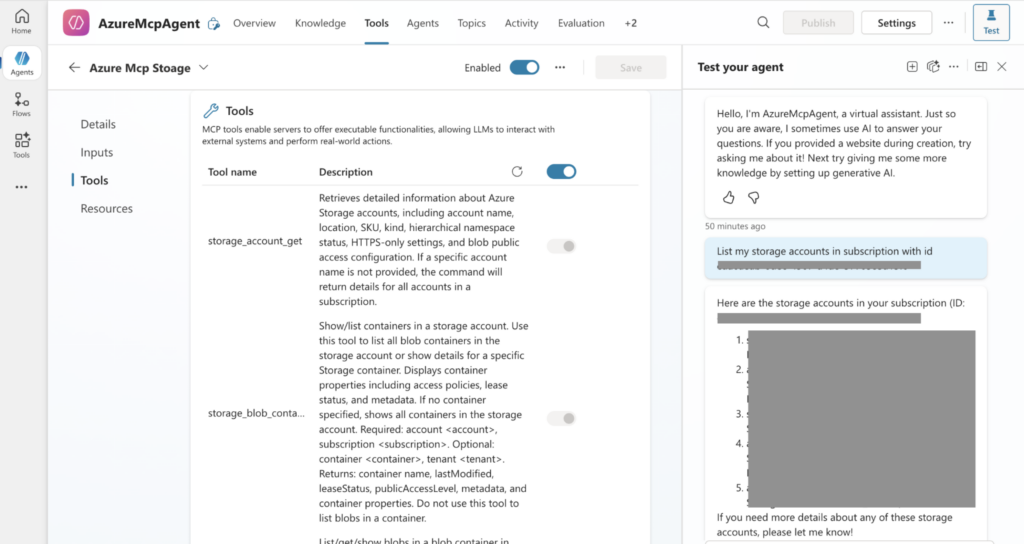
Source: Microsoft
5. FastMCP

FastMCP is a framework for building MCP servers and clients with built-in support for authentication patterns that align with MCP requirements. It abstracts common authentication challenges such as token validation, OAuth integration, and identity provider coordination, allowing developers to focus on application logic.
Key features include:
- Flexible authentication patterns: Supports API keys, JWT validation, and full OAuth 2.1 integration
- External identity provider support: Delegates authentication to OAuth and OpenID Connect providers
- Token validation mechanisms: Verifies JWTs using issuer, audience, and signature checks
- Dynamic client registration support: Enables automated authentication flows with compatible providers
- Multi-provider authentication: Combines multiple token sources into a single validation layer
How it meets the criteria:
- Architecture fit: Flexible for both local and remote MCP deployments, though more of a framework than a complete solution.
- IdP integration: Good support for external providers, but requires configuration and integration effort.
- Token management and scopes: Supports multiple token types and validation methods, though lifecycle management is not fully abstracted.
- Observability and auditing: Minimal built-in support; depends on external logging and monitoring systems.
- Security posture: Strong foundation with JWT and OAuth support, but advanced protections must be implemented separately.
- Developer experience: Relatively flexibility, but requires more hands-on implementation compared to managed solutions.
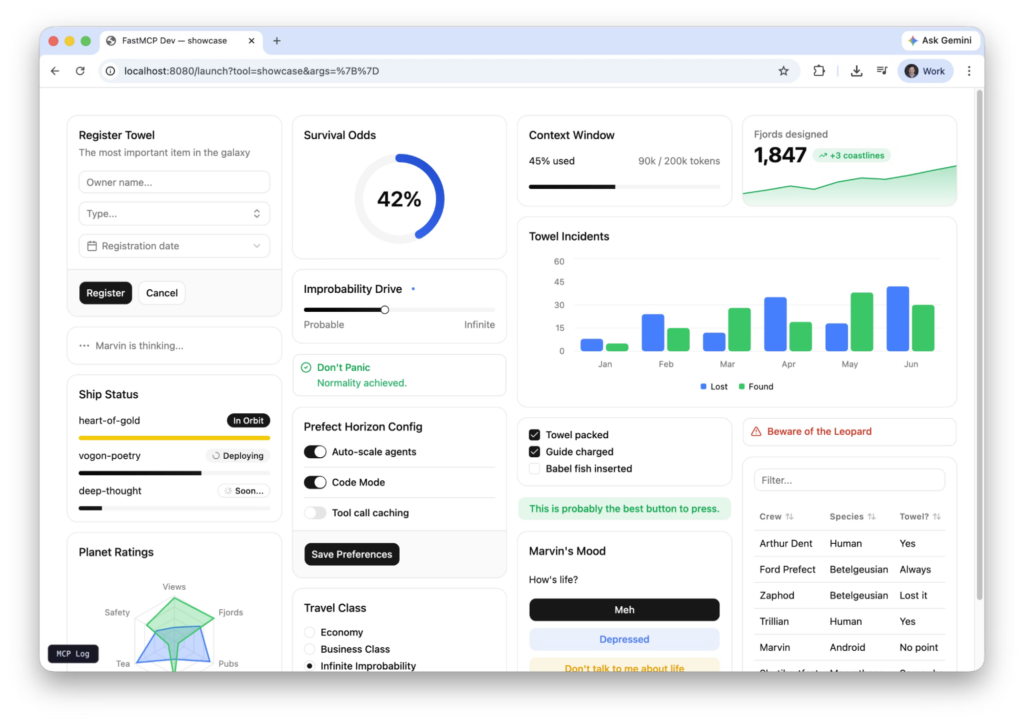
Source: FastMCP
Conclusion
Choosing an MCP authentication solution is primarily about aligning with standardized identity systems while maintaining control over access and permissions. Effective implementations separate authentication from authorization, rely on external identity providers when possible, and enforce fine-grained, token-based access control. As MCP adoption grows, the focus shifts from simply enabling connectivity to ensuring that every interaction between agents and systems is verifiable, scoped, and auditable.